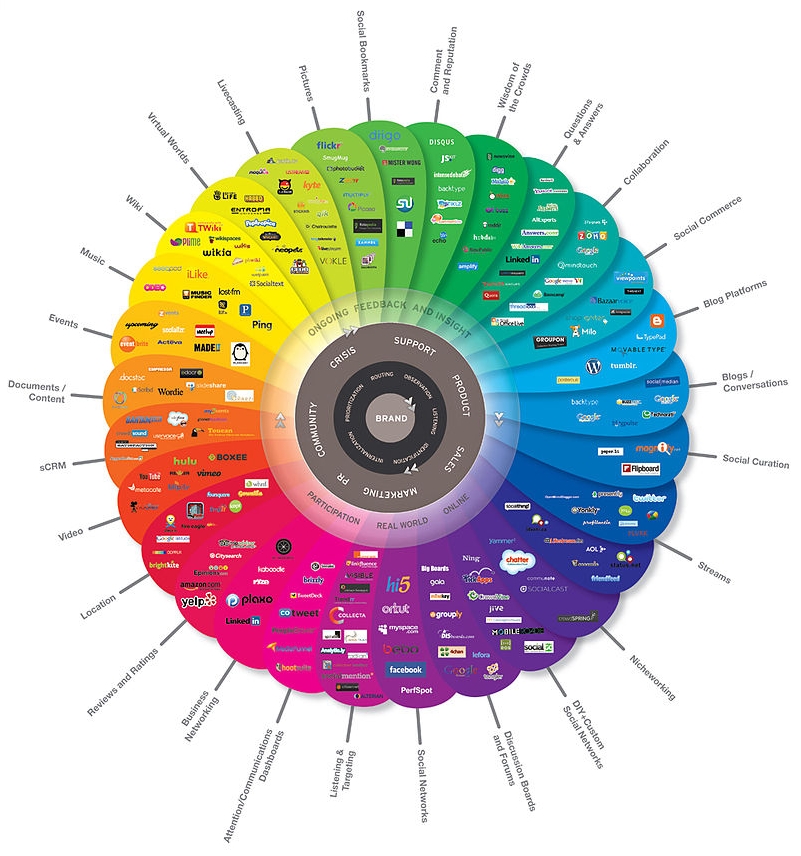
“Conversationprism” by Brian Solis and JESS3 – http://www.theconversationprism.com/. Licensed under CC BY 2.5 via Commons
The Weekly Writing Tips are a collection of best practices for writing and reporting at Global Voices. September's tips are brought to you by Rezwan, regional editor for South Asia.
We hear the question frequently: “How can you verify content from social media?” This arises because we often don't have personal relationships with the source, and therefore we have little reason to trust them. Lack of information about the users of social media (either in their profile or in the content) and virtual anonymity of sources makes us skeptical of the content they deliver.
Global Voices has its own guide to Verifying Social Media Content, but in this post I will highlight renowned writer and thought leader Patrick Meier's process of verifying social media data. It usually involves a two-step process:
- the authentication of the source as a real, trustworthy and reliable person
- assessing whether the content is valid and logical
If we can authenticate the source and find it trustworthy, this may be sufficient to trust the content and mark that it is verified, depending on the context. If source authentication is difficult to ascertain, then we need to triangulate the content itself.
If we are on Twitter, here are the suggested steps:
- Twitter profile: Look for name, picture, bio and any link to their own website/blog, professional occupation, etc. on their profile. Searching for the name or nickname on Google may provide further clues (Linkedin profile, Facebook page, etc.) to the person’s identity and may highlight news or blog posts about them.
- Number of followers: If the source has a large following it usually indicates that it's trustworthy. If there are only a few, look for the nature of the followers — whether they are credible or just spammers. Also important is to know how many lists the Twitter handle has been added to.
- Number of tweets: Is this a new Twitter handle with only a few tweets? New Twitter accounts can be created to spread disinformation, so be wary. If the Twitter handle has been around for a long time, you can check for evidence of political bias, misinformation, etc. You can further assess the nature of the tweets, whether they are intelligible, and look for exaggeration and inconsistencies in prior tweets to find out whether we can deduce that the content may be reliable.
- Number following: Check how many Twitter users the Twitter handle is following and the nature of them — look for political leaning, spams or bias and authenticated sources.
- Retweets: Check what type of content does the Twitter handle retweet. It also helps when the Twitter handle gets retweeted by known and credible sources.
- Location: This is a very important denominator. If the source’s geographic location be ascertained it helps to determine whether they are nearby the unfolding events. If they are tweeting from far away, it is more likely that they are quoting someone or doing something more nefarious. Also you can find out the person’s time zone by examining during which periods of the day/night the source tweets the most.
- Engage the source: If there are doubts, tweet the sources back and ask them for further information:
- Whether a photo or post belongs to the individual
- Who is in the photo or update
- What the photo or post is showing or saying
- Timing of the update or photo
- Location information
Now comes the second step. Let’s assume that we’ve gone through the steps above and could not find enough evidence to determine the authenticity of the source. Patrick Meier suggests some steps to triangulate the content. Here are some tips on how to do this:
- Triangulation: To start with, we need to remain skeptical about any content in social media. We should try to find whether there are multiple mentions of the event from different unconnected sources. Triangulation refers to the use of more than one approach to the investigation of a research question in order to enhance confidence in the ensuing findings. The more independent witnesses you can get information, the less critical the need for identity authentication.
- Indirect verification: Metadata that shows times, locations, identities and IP addresses of computer used to create social media evidence.
- Origins: If the user reporting an event is not necessarily the original source, can the original source be identified and authenticated?
- Common sense: Use common sense in evaluating the content — whether the shared picture or the language of the content contains some inconsistent elements.
- Social authentication: Ask members of your own social network whether the tweet you are investigating is being reported by other sources. Ask them how unusual the event reporting is to get a sense of how likely it is to have happened in the first place.
- Follow up: If you have contacts in the geographic area of interest, then you could ask them to follow up directly or in person to confirm the validity of the report if necessary.
While highlighting a tweet in a GV post, it's important to include more than just the user's handle. Date and time of the tweet in relation to the event, location, biographical information and online characteristics (prolific Twitter user?) are all good details to include because they add credibility. Avoid embedding retweets — find the original tweet and use that instead.
Other resources:
- Global Voices guide How to Verify Social Media Content
- If a social media content has been posted by a real person, we can usually safely assume that it is more credible rather than content from a fake or hoax account. Pipl can help to track down a person's profile on other social networks. Public records are also available on sites like 192.com.
- Verification handbook is a definitive guide to verifying digital content for emergency coverage.
- Are you a journalist? Download this free guide for verifying photos and videos by First Draft
- How to verify information from tweets by Steve Buttry
- How to: verify content from social media
- “How to Separate Fact and Fiction Online”: 2012 TED talk from Markham Nolan of Storyful.
- Read how Andy Carvin does crowdsourced verification and turns his Twitter feed into a real time newswire.
- More tips from Journalist's Resource and Verification Junkie.



1 comment